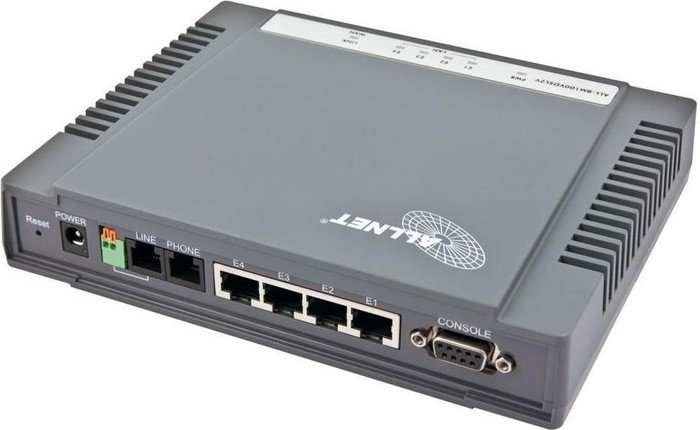
VDSL Client Modem ALL-BM100VDSL2: Broken Authentication and Default Root User
Date: 2017-04-13 14:01:411. Introduction
| Affected Product: | VDSL Client Modem ALL-BM100VDSL2 C.4.6a |
| Fixed in: | C.4.8a |
| Fixed Version Link: | http://www.allnet.de/nc/de/allnet-brand/support/treiber-firmware/download/120183/ |
| Vendor Website: | http://www.allnet.de/ |
| Vulnerability Type: | Broken Authentication & Default Root User |
| Remote Exploitable: | Yes |
| Reported to vendor: | 12/20/2016 |
| Disclosed to public: | 04/13/2017 |
| Release mode: | Coordinated Release |
| CVE: | n/a (not requested) |
| Credits | Tim Coen & Marcus Gruber of curesec GmbH |
2. Overview
The authentication of the web interface of the VDSL Client Modem ALL-BM100VDSL2 relies on local IP addresses and can thus be bypassed by an attacker with access to the local network as long as any user is currently authenticated. Additionally, the system contains an undocumented default user with a hardcoded password who has root access to the device.
3. Details
Broken Authentication
CVSS: High 8.8 CVSS:3.0/AV:A/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H
The application does not contain proper session management or authentication. Instead, authentication is based on the IP address that is used to log into the web interface. Thus an attacker that is registered in the local network can send arbitrary requests to the web interface if any user is currently logged into the web interface, as long as the attacker has assigned themselves the same local IP address.
An attacker could for example add a new user. With this user they could - after enabling telnet access in the web interface - connect to the application via telnet and thus have complete control over it.
Default Root User
CVSS: High 8.8 CVSS:3.0/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
It is possible to connect to the device via telnet as well as the web interface using the default credentials support_user:support_user. The support user has root access and thus full control over the device.
The documentation mentions the default user admin:admin prominently, and recommends changing the admin password. However, it does not mention the support_user and does not recommend changing the password of that user alongside the admin user.
4. Solution
To mitigate this issue please upgrade at least to version C.4.8a:
http://www.allnet.de/nc/de/allnet-brand/support/treiber-firmware/download/120183/
Please note that a newer version might already be available.
5. Report Timeline
| 12/20/2016 | Informed Vendor about Issue |
| 12/23/2016 | Vendor announces release of new firmware |
| 02/15/2017 | Reminded Vendor about disclosure date |
| 03/01/2017 | Vendor releases new Version |
| 04/13/2017 | Disclosed to public |


